Evernote uses the secure and widely adopted industry standard Security Assertion Markup Language 2.0 (SAML 2.0). This means that our implementation of SSO integrates easily with any large identity provider that support SAML 2.0. We also support ADFS.
Supported Identity Providers
To make setup easy, we’ve partnered with several identity providers, including Ping Identity, OneLogin, Okta, and Centrify. Because Evernote uses SAML 2.0, you can use SSO with any SAML-supported identity provider.
Enable SSO from the admin console
To configure SSO:
- Sign in to the admin console.
- Click Single Sign-On from the navigation menu.
- Enter the SAML HTTP Request URL (the link used to verify SSO).
- Enter the X.509 Certificate from your SAML authentication.
- Enter a 'Session Duration' (the number of days you want the SSO token to remain valid before your employees will have to re-authorize their token again). Note: The default value is 1 (days). It’s a good idea to configure this to a value greater than 1.
- Click Save & Enable.
Notes:
- For Evernote Teams accounts that have not been updated: When you enable single sign-on, users of your Evernote Teams account will need to authenticate using your SAML identity provider before they are allowed to access team content. Evernote Teams account admins will be allowed to sign in to Evernote Web and the admin console without going through single sign-on. For Evernote Teams accounts that have enabled SSO, users will first be prompted to log in with their Evernote credentials, then the SAML authentication process will take place for their team content.
- For Evernote Teams accounts that have been updated: The identity provider has its own setting for when a user will need to re-authenticate their SSO token.
- Only Evernote Teams account admins are authorized to configure single sign-on (SSO) for the team.
Frequently Asked Questions
Which identity providers does Evernote support?
Evernote uses the secure and widely adopted industry standard Security Assertion Markup Language 2.0 (SAML 2.0). Our implementation of SSO integrates easily with any large identity provider that supports SAML.
We’ve partnered with the following identity providers:
- Ping Identity
- OneLogin
- Okta
Other identity providers we support:
- Centrify
- Symplified
- Auth0
- CA Siteminder
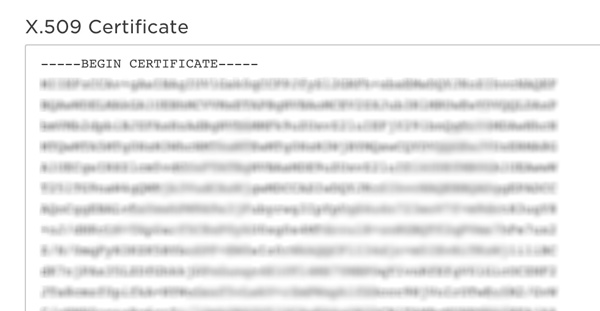
What’s an X.509 certificate?
An X.509 certificate is a security certificate that's used to verify your identity. It usually comes from your identity provider. It can come in a variety of formats, but Evernote only accepts the .pem format. Below is a sample of an encoded certificate:
How are people notified when SSO is enabled?
Once you enable SSO for your Evernote Teams account, the account admins should send an email to notify team members that SSO has been enabled.
What happens when an employee joins the account?
If your account has configured SSO as a requirement, the new employee’s email address needs to be registered with your identity provider. Otherwise, they will not be able to sign in and access Evernote.
How does SSO work with two-step verification?
If your company has decided to make SSO a requirement, authentication will be determined by the identity provider they’ve chosen to use. Your company can always add more layers of security through the identity provider. Any security features that Evernote itself provides, such as two-step verification or the ability to reset passwords, are no longer in effect because the identity provider now handles all aspects of authentication.
How do users sign in to Evernote using SSO?
Click here to see the steps to sign in with SSO.
Keywords:
- configure sso
- enable sso
- security
- set up sso
- single sign on
- single sign-on
- sso
Updated